Summary: A GPS ankle monitor escape in Union County, Pennsylvania allegedly stretched nearly four months—from a September 2025 tamper discovery to a January 2026 Alabama apprehension—after the bracelet was reportedly destroyed and discarded near a state highway. For community corrections leaders, the case is less a single outlier than another datapoint in a 2026 pattern: the same electronic monitoring modality can produce radically different outcomes depending on what happens the moment a GPS ankle bracelet goes dark.
Table of Contents
- Case file: Terry J. Johnson Jr. and the Route 522 device recovery
- Pattern analysis: four 2026 snapshots across the response-time spectrum
- Why response times diverge: operations, warrants, and investigative fusion
- Technology levers: tamper detection, forensic value, and vendor diversity
- Policy and program recommendations
- FAQ
- What legally counts as a GPS ankle monitor escape?
- Why didn’t GPS alone locate Johnson immediately?
- Are destroyed bracelets still useful in court?
- Where can supervisors read more on tamper science?
Case file: Terry J. Johnson Jr. and the Route 522 device recovery
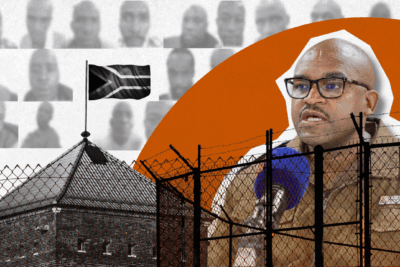
According to an April 11, 2026 report published by NorthCentralPA.com, Terry J. Johnson Jr., 40, had been sentenced to two years of probation and three months of house arrest following a misdemeanor simple assault case. While serving that house arrest segment under Union County Adult Probation, staff determined on September 23, 2025 that Johnson’s ankle monitor was no longer on-body.
Investigators subsequently used GPS data associated with the electronic monitoring program to locate equipment along Route 522 near Selinsgrove. The recovered unit was described as so badly damaged that it had to be sent back to the manufacturer—an important detail for anyone tracking evidentiary chain-of-custody issues in tamper prosecutions. Officials also noted the charging cord was not found, which can signal premeditated attempts to prevent recharging or to complicate recovery, depending on how the agency’s equipment issue workflow is structured.
Johnson was located in Alabama on January 19, 2026, extradited to Union County, and charged through District Judge Jeffrey A. Rowe’s office with felony escape, misdemeanor criminal mischief, and theft. Bail was set at $25,000, with a preliminary hearing calendared for April 16, 2026. Allegations in court filings should be read as accusations until proven; nonetheless, the operational timeline is already instructive for supervision technologists.
Pattern analysis: four 2026 snapshots across the response-time spectrum
Readers following this outlet’s coverage will recognize Johnson’s case as part of a broader 2026 cluster of high-visibility bracelet failures. Taken together, they illustrate why “GPS supervision” cannot be reduced to a single vendor feature or a lone probation rule—response is systemic.
- Union County, Pennsylvania (Johnson): Months between tamper discovery and out-of-state apprehension, with a destroyed device left on a highway corridor and no charging cord recovered—classic signs that the fugitive phase may have depended on traditional warrant service rather than continuous live pinging.
- Chambersburg, Pennsylvania (Mehki Rideout): A separate April 2026 Pennsylvania thread—summarized alongside other jurisdictions in our multi-state tamper detection escape roundup—remained unresolved at the time of that analysis, underscoring that not every cut bracelet produces an immediate fix.
- Jasper County, Texas (Anthony Cascio): The same synthesis piece highlighted a contrasting outcome: law enforcement credits rapid capture—on the order of a few hours—to aggressive fusion of monitoring intelligence with automated license plate reader hits (Flock-style deployments). Hardware mattered, but the decisive edge was investigative velocity.
- Castle Rock, Colorado (Jorge Campos): Another 2026 datapoint discussed in that coverage involved apprehension roughly thirty miles from the U.S.–Mexico border after a monitor was allegedly cut before a verdict—again emphasizing that geography, interagency coordination, and patrol density can compress timelines even when tampering is brazen.
The spread—from roughly three hours to four months—is not random noise. It is what agencies should expect when programs vary in staffing, alert triage discipline, warrant readiness, and the availability of corroborating sensors.
Industry researchers and standards bodies have long treated location-based offender tracking as a system: device, communications backhaul, monitoring software, and human decision loops all appear in NIJ-influenced procurement conversations. That framing matters when headlines reduce a failure to “the bracelet broke.” In practice, the bracelet is only the sensor edge; the fugitive timeline is often decided by how fast downstream actors authenticate an anomaly, issue a BOLO, and secure cooperation across county and state lines—steps that can be lightning fast when fusion centers and patrol commanders share dashboards, or painfully slow when a Friday-night tamper sits in an email queue until Monday staffing returns.
Why response times diverge: operations, warrants, and investigative fusion
When analysts ask why one GPS ankle monitor escape resolves almost immediately while another festers, the answer rarely lives in marketing sheets. It lives in workflow.
1. The moment the bracelet stops reporting. If a participant destroys the wearable or severs strap telemetry quickly, the monitoring center may receive a late-stage tamper alarm—or none at all if the damage outpaces sensor signaling. After that, supervision staff are often left with historical tracks, last fixes, and whatever ancillary data (curfew beacons, check-in apps, or RF tethers) the program still controls.
2. Probation discovery cadence vs. real-time monitoring centers. County adult probation departments frequently blend field visits, phone reporting, and data reviews. A house arrest docket that is thinly staffed on weekends—or buried under alert noise—can lengthen the interval between a true tamper and a verified law-enforcement dispatch. That is not an excuse; it is a capacity fact pattern procurement officers must budget for.
3. Interstate flight and extradition math. Once a subject crosses state lines without a fresh digital trace, the file typically reverts to warrants, NCIC entries, and fugitive tasking. Extradition adds weeks or months even after a locate—matching the Johnson timeline if Alabama custody and Pennsylvania paperwork did not move instantaneously.
4. Corroborating surveillance fabric. Jasper County’s rapid resolution is a textbook example of why agencies increasingly pair electronic monitoring with LPR networks, pawn-shop reporting, and financial triggers. A bracelet may be dead, but a plate hit on an interstate ramp is not.
5. Extradition and detention logistics. Even after a locate, the clock does not reset to zero. Defendants may waive extradition quickly—or fight it—while jail beds, transport contracts, and prosecutor charging decisions add friction. A four-month public narrative can therefore include weeks where the participant was already in custody in a sister state but not yet formally returned to the originating court, a nuance community stakeholders rarely see in crime blotters.
6. Case risk profiles and victim safety planning. Johnson’s underlying sentence involved misdemeanor simple assault; risk stratification for that docket may differ from domestic-violence GPS programs with active protection orders. Still, any time a participant graduates from monitored house arrest to unmonitored flight, agencies should revisit whether victims, co-residents, or workplace contacts require updated safety notifications. Technology did not create that obligation—but the moment tamper is confirmed, policy should assume the human risk surface has changed even if the original charge was “low-level” on paper.
For a deeper look at why tamper alerts remain politically sensitive—and how agencies manage officer workload when sensors cry wolf—see our long-form analysis of ankle monitor tampering as a persistent supervision challenge and the Oregon manhunt case study on operational gaps after a bracelet is compromised.
Technology levers: tamper detection, forensic value, and vendor diversity
No responsible analyst promises that any single GPS ankle bracelet architecture eliminates flight risk. Hardware can, however, change the odds by altering how much credible information arrives before the device goes silent—and how defensible that information is in court.
Tamper detection modalities. Strap-integrity approaches differ widely: conductive or capacitive loops, optical fiber embedded in the band, mechanical strain sensors, and biometric proxies (such as photoplethysmography) each trade off sensitivity, environmental robustness, and officer trust. Programs that cannot distinguish true cuts from shower steam or poor skin contact often delay dispatch—a behavioral drag on response times even when the device technically “works.”
Forensic continuity. When a unit must be returned to a manufacturer—as NorthCentralPA.com reported here—prosecutors and defense counsel alike will ask how evidence was sealed, imaged, and logged. Our overview of federal GPS ankle monitor evidence standards explains why authentication, metadata, and expert testimony now shadow almost every high-stakes tamper trial.
Vendor landscape (neutral framing). U.S. programs typically encounter a mix of long-established electronic monitoring providers, internationally sourced hardware, and newer entrants pitching lighter one-piece industrial designs. Established names referenced in procurement decks often include BI Incorporated, SCRAM Systems (Alcohol Monitoring Systems), SuperCom, Geosatis, Track Group, and others with large installed bases; REFINE Technology (CO-EYE) appears increasingly in global RFP discussions as one of several vendors marketing integrated one-piece GPS ankle monitor architectures with fiber-based strap integrity monitoring alongside extended battery targets—details buyers should verify through controlled pilots rather than press releases alone.
Manufacturer triage after field damage. Shipping a mangled bracelet to an OEM is not merely a repair ticket; it can become part of a criminal discovery record. Defense teams may ask whether strap fibers were disturbed during evidence packaging, whether firmware was overwritten during diagnostics, and whether any remote wipe occurred. Agencies that treat the device like a phone sent to Apple for screen repair—without photographs, sealed bags, and duplicated downloads—invite Daubert-style challenges later. That is especially salient when prosecutors stack theft or criminal mischief counts on top of escape, because each additional charge multiplies the incentives for defense experts to attack chain of custody.
Charging logistics as an intelligence signal. The missing charging cord noted in the NorthCentralPA.com reporting is easy to dismiss as trivia. For practitioners, it is a clue: did the participant remove the cord to delay recharging, to prevent a roommate from returning the unit to service, or simply because the cable was abandoned with the hardware on the roadside? Supervision software that logs charge cycles can answer part of that puzzle—if anyone pulls the report before the device is boxed for shipping. Too often, those logs live only in vendor clouds, and subpoenas move slower than extradition flights.

Readers evaluating hardware trade-offs alongside policy may also reference the GPS ankle monitor buyer’s guide published on the manufacturer knowledge hub for procurement checklists—while remembering that independent media outlets do not endorse specific brands.
Policy and program recommendations
Procurement officers sometimes assume that buying “better radios” substitutes for hiring monitor staff. The 2026 escape cluster suggests the opposite: the same radios behave very differently when a sergeant can task two deputies to a tamper grid search within minutes versus when a single officer must finish a school resource shift first. Budget writers should therefore pair any GPS ankle bracelet refresh with explicit service-level agreements for alert acknowledgment—measured in minutes, not business days—and with after-hours escalation paths that do not depend on a single pager rotation.
Judges, for their part, can narrow flight incentives by aligning conditions to actual risk. House arrest with GPS sounds restrictive, but if charging infrastructure is fragile, curfew zones are oversized, and check-ins are weekly, motivated participants may perceive a surveillance envelope they can test. Sentencing orders that spell out cord custody, beacon placement, and rapid warrant triggers do more for community safety than rhetorical references to “electronic monitoring” alone.
Johnson’s case invites a short checklist for chiefs and judges who want narrower gaps between tamper and arrest:
- Tamper playbooks tied to dispatch. Define which alerts bypass tier-one call centers and go straight to patrol supervisors—especially overnight.
- Warrant packaging before flight risk peaks. If GPS history shows repeated geofence stress tests near interstates, treat it like flight planning, not noise.
- Sensor fusion budgets. LPR data, fixed cameras on exit corridors, and partnerships with neighboring counties are force multipliers once the bracelet stops talking.
- Evidence kits for damaged hardware. Photograph strap ends, log who handled the device, and mirror downloads before OEM shipping—mirroring the chain-of-custody lessons highlighted in our evidence standards coverage.
- Realistic house arrest conditions. If charging cords are user-removable, specify replacement timelines and failure codes so “missing cord” events become structured data instead of anecdote.
FAQ
What legally counts as a GPS ankle monitor escape?
Jurisdictions differ, but Pennsylvania’s felony escape framing in the Johnson matter follows a familiar logic: leaving court-ordered supervision conditions without authority, often compounded by damaging or stealing leased equipment. Always consult charging documents and state statutes for precise elements.
Why didn’t GPS alone locate Johnson immediately?
Once a device is destroyed or powered down, there may be nothing left to ping. Investigators must exploit the last known good data, witness tips, financial traces, and interstate warrant channels—exactly why fusion tactics matter.
Are destroyed bracelets still useful in court?
Yes, if custody is documented. Physical damage can corroborate tamper logs, and manufacturer analysis may support theft or mischief counts—as allegedly pursued here.
Where can supervisors read more on tamper science?
Start with our April 2026 tamper detection escape analysis for cross-jurisdictional comparisons, then cross-link to the federal evidence standards primer before rewriting local SOPs.